#170: Short Takes: The security of Pix and PSTIs, and how hacker attacks resulted in new regulations
W FINTECHS NEWSLETTTER #170
👀 Portuguese Version 👉 here
👉 W Fintechs is a newsletter focused on financial innovation. Every Monday, at 8:21 a.m. (Brasília time), you will receive an in-depth analysis in your email.
This edition is brought to you by
With more than 40 years of experience, Futurex is a global leader in cryptographic and data‑protection solutions, specializing in developing Hardware Security Modules (HSMs) and cryptographic management platforms that enable high levels of control, security, and regulatory compliance.
Its solutions protect critical information and digital transactions. The company stands out for promoting cryptography as a strategic business enabler, anticipating technological trends, and supporting organizations in building secure, resilient, and future‑ready digital environments.
Welcome to the Short Takes edition! As the name suggests, unlike deep dives, these editions will explore a variety of topics that might later evolve into full deep-dive editions.
Short Takes is designed for entrepreneurs, investors, and operators looking for quick, actionable insights.
In December, W Fintechs released a report on the 5 years of Pix (link to the EN version, here ). In just five years, the system reached more than 160 million users, connected 800+ institutions, processed 200 billion transactions, and moved more than R$ 80 trillion. These numbers alone already say a lot, but they gain even more meaning when observed over time.
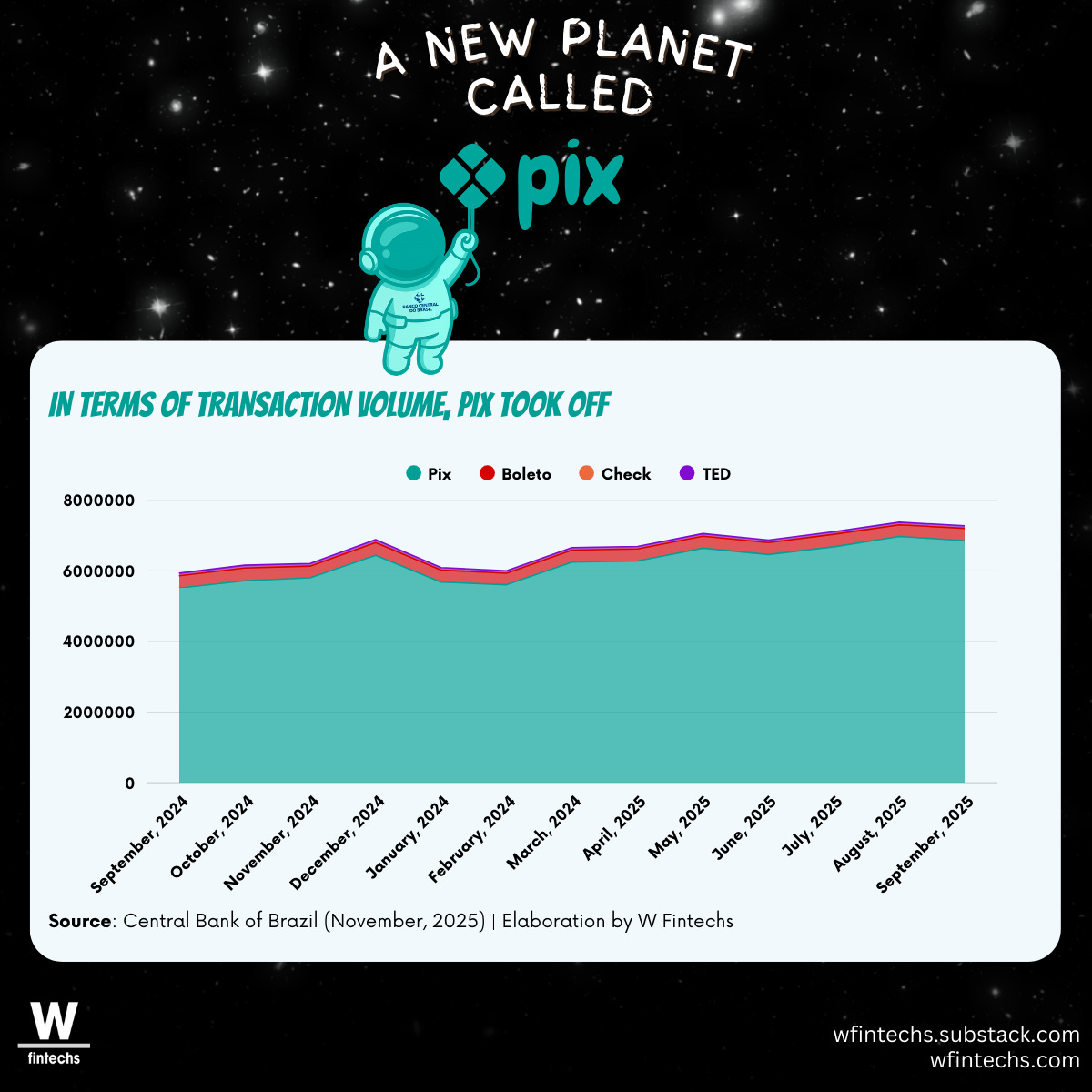
When looking at the recent series of transactional volumes, between September 2024 and September 2025, it becomes clear that Pix not only surpassed traditional instruments, but also came to consistently occupy the center of the payments infrastructure.
This scale helps explain why Pix has also come to occupy the center of the debate on risk and security. Recent cases widely reported in Brazil, such as the attack on C&M Software, which resulted in estimated losses of hundreds of millions of reais, in addition to incidents involving smaller service providers with losses in the tens of millions, gained even more relevance both in the news and for the regulator.
The attacks, attributed to Pix, were quickly framed in the public debate as failures of the instant payments system itself, when in practice they reveal something quite different. The Pix core, operated by the Central Bank through the SPI (Instant Payments System), remained intact and available throughout all the episodes. What was exploited, however, was not the heart of the payment system, but its operational surroundings, composed of intermediaries, technology providers, and access chains that have become, over time, essential to the scale of the model.
There is a fundamental difference between attacking a centralized system, designed with rigorous governance controls, and exploiting the intermediaries that orbit this system. In the first case, the hacker needs to break through different layers of security, encryption, and monitoring. In the second, it is enough to find a link with lower maturity, where processes, people, and controls have not evolved at the same pace as the technology. This is what happened in the reported cases.
Technology service providers (PSTIs) assumed a structurally relevant role in the Pix ecosystem, mainly to allow smaller institutions to access the system. By connecting dozens of smaller institutions to the Brazilian Payments System, they became true access hubs to the instant settlement enabled by Pix. This operational centrality brought efficiency, reduced entry barriers, and accelerated financial inclusion, but it also created new potential points of failure.
A common element in almost all of the episodes was the use of valid credentials. There was no breaking of encryption, no direct intrusion into the SPI, and no exploitation of flaws in the Pix protocol. The hackers, in fact, entered through the front door, using legitimate keys obtained through social engineering, abuse of trust, or failures in internal governance. The system, upon receiving correctly signed orders, did exactly what it was designed to do. It was precisely from this point that the regulator began to broaden its focus to PSTIs, recognizing that the problem was not in the functioning of Pix itself, but in the conditions of access to its architecture, in the governance of intermediary environments, and in the requirements imposed to operate this infrastructure.
The architecture of Pix
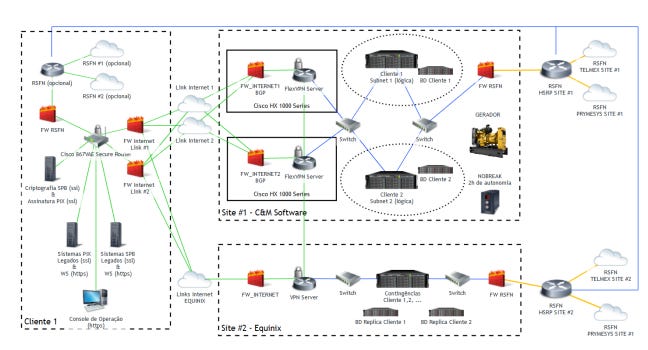
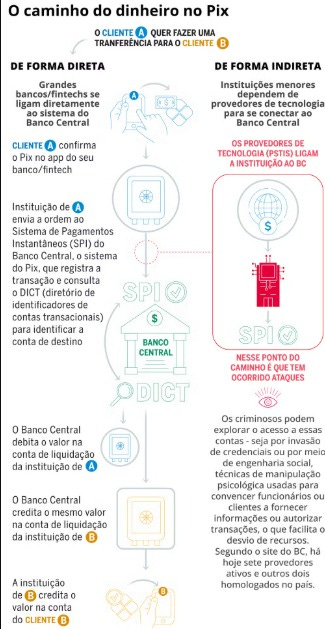
The architecture of Pix was designed to be simple and instantaneous in settlement from day zero, and above all to allow access by different institutions. The design of the SPI assumes an environment of high institutional trust, in which authorized participants interact directly with the Central Bank.
From this design, the way an institution accesses Pix begins to shape the real differences in responsibility, control, and risk throughout the system. Institutions with direct access to the SPI operate under a stricter regime of controls, governance, and operational responsibility, while indirect participants depend on technology service providers to intermediate their relationship with the Central Bank.
Documents from C&M Software from 2020, for example, show that this intermediated access was structured based on a logic of isolation and operational trust, in which each client institution operated in segregated tunnels, with its own certificates and dedicated controls, while the PSTI, in this case C&M, assumed the role of a messaging and connectivity hub with the RSFN (the financial system network) and later with the SPI. The arrangement sought to keep the core protected and, at the same time, create room for the expansion of the system, without pushing the full cost of operating directly with the Central Bank onto each participant.
The intermediary layer has always been part of Pix’s architecture to enable scale, reduce entry barriers, and allow smaller institutions to access the system without operating directly in the SPI. This arrangement was decisive for the rapid expansion of Pix and for the diversity of participants it reached. What changed after the recent episodes was the weight this layer began to carry as the number of connected institutions grew and new operational models, such as BaaS, became established.
In the cases of attacks against different PSTIs, the exploited vector was precisely this intermediary link: a PSTI that concentrated access for multiple institutions, where valid credentials and administrative privileges were improperly used to trigger signatures that, from the SPI’s perspective, were legitimate. The system responded as it always had, executing correctly signed orders.
Reserve accounts are where this dynamic materializes most concretely. Because Pix settles in real time, any validly signed order produces immediate and irreversible effects. During the attacks, amounts were debited directly from these accounts, held at the Central Bank, which means that the Central Bank executed transactions that were technically correct, even when the improper use of credentials was later identified.
The regulator’s responses and the new limits of Pix
It was from this reorganization of risk, and not from a technical failure of Pix, that the regulatory response gained momentum. The Central Bank reacted by imposing transactional limits, anticipating licensing requirements, and reinforcing security obligations. These were necessary measures given the severity and financial impact of the episodes, but they also expose a recurring trait of financial regulation: it tends to advance more rapidly when risk stops being a distant hypothesis and becomes materialized in concrete losses.
Throughout 2025, this response began to translate into rules that reflect a broader reading of Pix’s real functioning. Without eliminating the formal distinction between direct and indirect participants, the regulator began to bring closer the requirements applicable to indirect operations, especially in cases where system access depends on technological intermediaries. More restrictive limits for access via PSTIs, stricter segregation of credentials, restrictions on the sharing of private keys, and additional message validation requirements indicate an important shift. Dependence on third parties ceased to be seen merely as an operational convenience and started to be treated as part of the arrangement’s risk surface.
In this context, technology service providers began to occupy a clearer place in the regulatory equation. They have always been part of the ecosystem’s functioning, enabling access, connectivity, and operation for a relevant share of participants. What changes now is not their function itself, but the recognition that this role carries responsibilities consistent with the position they occupy in the system’s real architecture. In an arrangement based on chains of access, credentials, and privileges, the level of governance required needs to keep pace with the degree of operational centrality these agents have come to exercise.
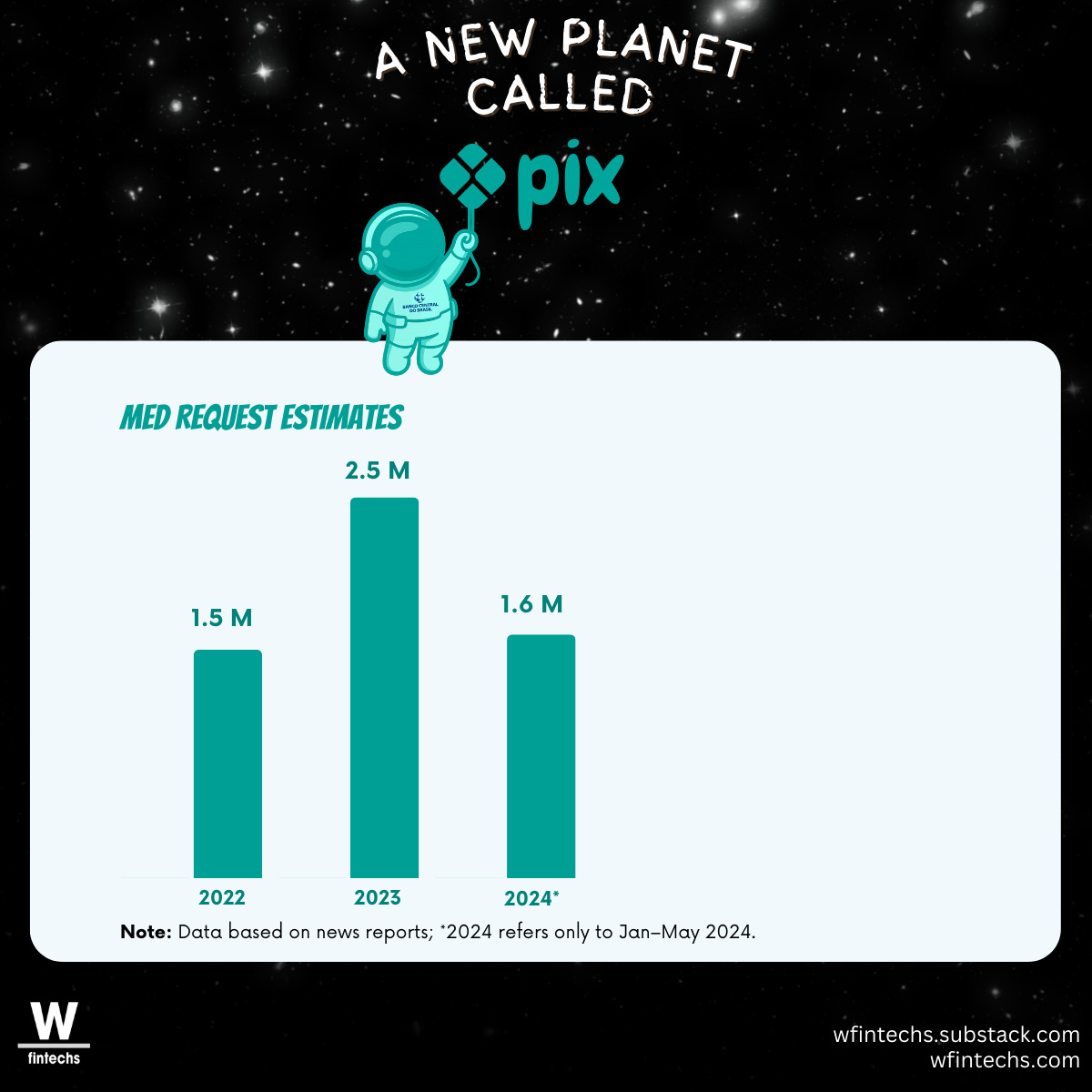
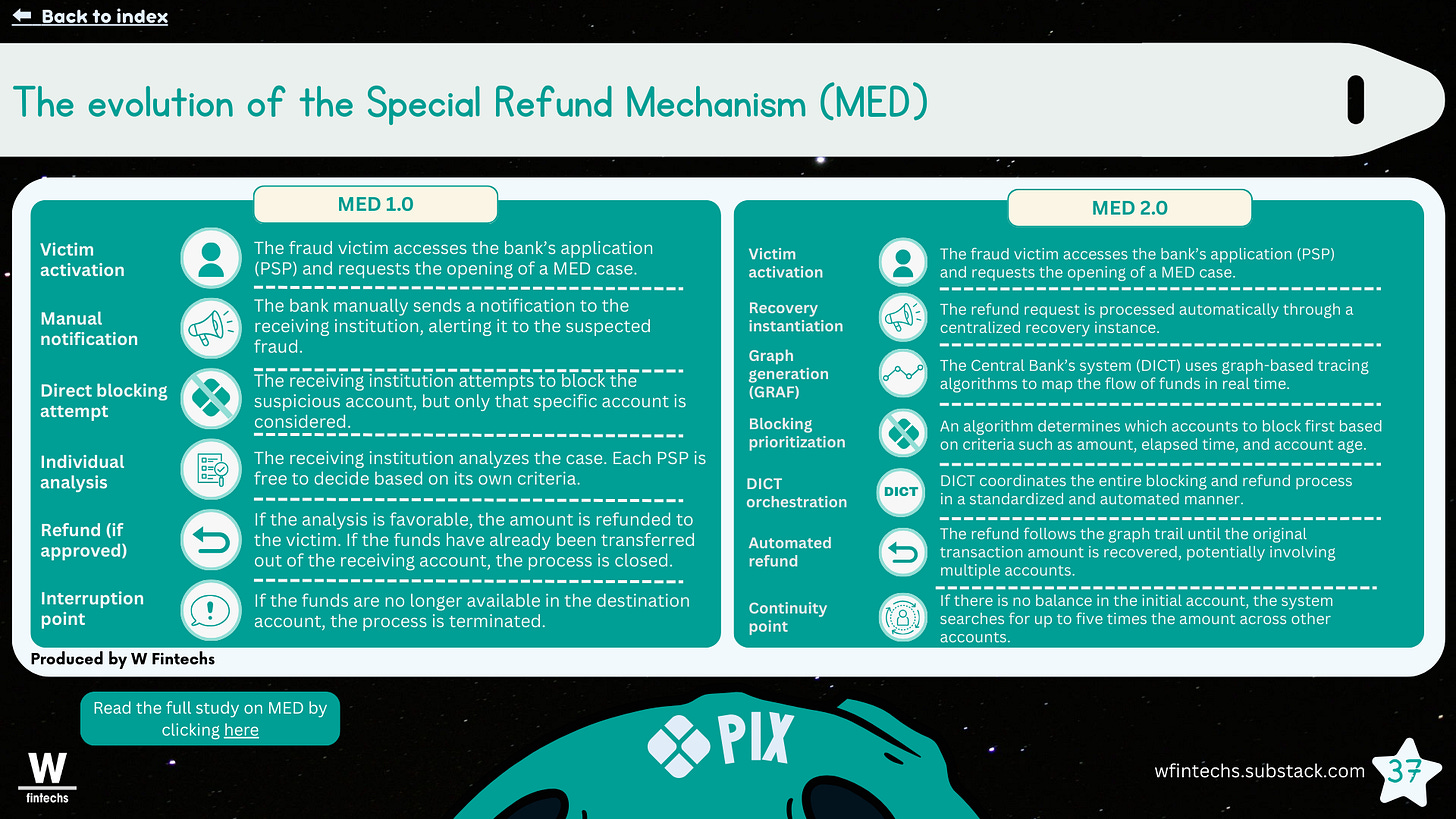
The strengthening of the Special Return Mechanism fits into this same movement and helps to size the scale of the problem. Data compiled in the Pix study by W Fintechs show that the volume of requests via MED can no longer be treated as an operational exception: there were around 1.5 million in 2022, 2.5 million in 2023, and more than 1.6 million in just the first months of 2024.
At the same time, these numbers help to understand the path the Central Bank has begun to follow. The MED (Special Return Mechanism) emerges as an attempt to reduce the fragmentation that existed until then, when each institution independently decided how to handle the reimbursement of funds in cases of fraud. The move points to greater coordination in an instant system, with flow tracing, faster blocking, and structured efforts to recover resources before they disperse, a topic addressed in edition #152.
In this context, the discussion around security moves beyond a purely regulatory dimension and also requires dedicated cryptographic technologies. Companies such as Futurex operate precisely at this level. Their physical and cloud based HSMs, integrated with CryptoHub for centralized key management, allow banks and technology service providers to keep critical keys and data isolated within certified hardware, in alignment with standards such as PCI DSS and PCI PIN v3. Rather than treating security as an additional layer, the approach is to structure cryptographic custody as the core of the operation, reducing exposure to clear text keys and organizing credential management in an auditable and centralized manner.
Even so, as sophisticated as it may be, the MED continues to act after settlement has already occurred. In the episodes mentioned above, the impact was not at the level of the end user, but in the reserve accounts maintained by institutions at the Central Bank, which are used exclusively for settlement among Pix participants. When validly signed orders reach this level, the debit occurs immediately and definitively. In a system designed to operate in real time, the interval between order execution and the dispersion of resources is too short for any subsequent response to be fully effective. What these episodes make clear is that the center of the discussion lies before settlement, in the environment where orders are issued, where keys and credentials are stored, used, and supervised. It is in this terrain that regulation begins to play a less reactive and more structural role, not as an obstacle to innovation, but as a condition for systemic trust, across all parties involved, to keep pace with the scale that Pix has already achieved.
Until the next!
Walter Pereira
If you know anyone who would like to receive this e-mail or who is fascinated by the possibilities of financial innovation, I’d really appreciate you forwarding this email their way!
Disclaimer: The opinions expressed here are solely the responsibility of the author, Walter Pereira, and do not necessarily reflect the views of the sponsors, partners, or clients of W Fintechs.